What is VPN Site to Site? What is VPN Client to Site? Simply understood, VPN Client to Site helps individuals securely connect to a corporate network, while VPN Site to Site creates a secure tunnel between two networks, allowing branches to work as one. Join Antidetect Browser Hidemyacc to explore how it works and the benefits of VPN Site to Site in this article!
1. What is VPN Site to Site?
What is VPN Site to Site? is an important question that helps you better understand secure connection solutions between networks, allowing an enterprise's offices, branches, or datacenters to link with each other through an encrypted tunnel.
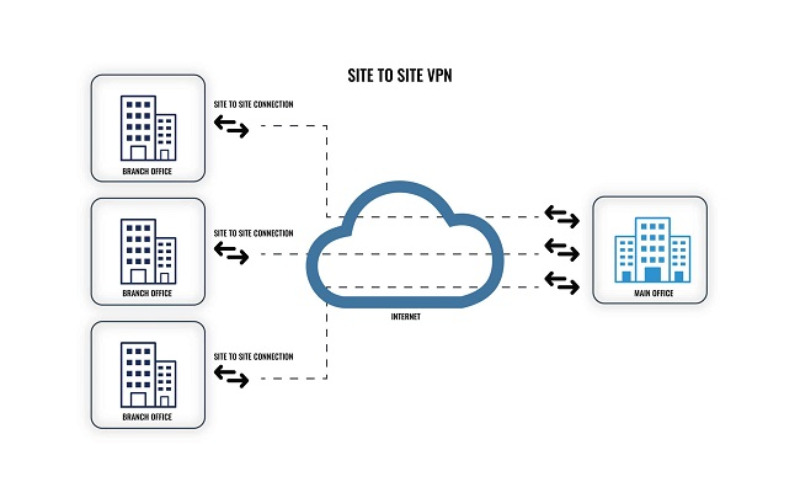
What is VPN Site to Site?
Thanks to VPN Site-to-Site, organizations not only enhance security but also optimize performance and maintain business continuity.
2. What is VPN Client to Site?
VPN Client-to-Site is a secure connection solution that allows users to access a corporate network remotely via VPN software on their personal devices. This connection creates an encrypted tunnel, protecting exchanged information and data even when users are on unsecured public Wi-Fi networks.
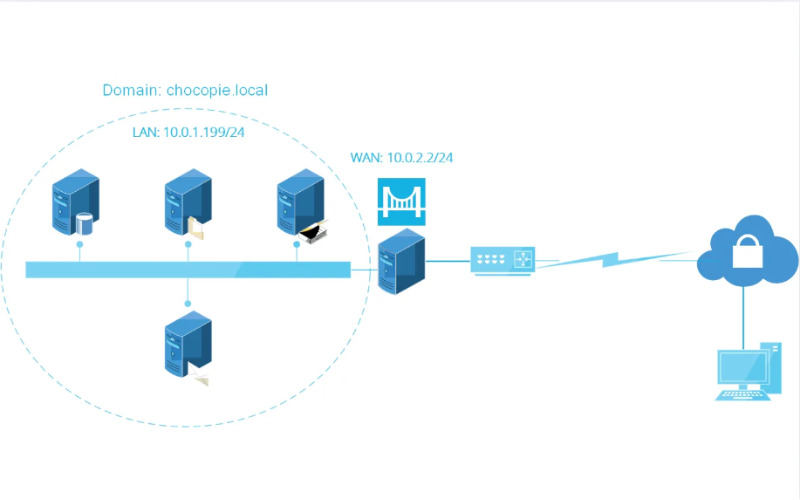
This solution is particularly useful for remote work, helping employees easily access company resources without worrying about cyber attack threats. Popular protocols supporting VPN Client-to-Site include PPTP, L2TP, IPsec, and SSL/TLS, with each protocol providing different levels of security and performance depending on connection needs.
>>>> LEARN MORE:
- What is Radmin VPN? Download latest free Radmin 2026
- Shadowrocket là gì? Simple installation and usage 2026
3. How VPN Site to Site works
The VPN Site-to-Site protocol creates an encrypted tunnel between networks at different locations, helping data travel over the Internet safely and securely. This tunnel acts as a protective link, allowing information to be transmitted without fear of intrusion or external disruption.
Data is guided through the tunnel via a routing table, with the support of strong encryption protocols to prevent access or tampering by malicious actors. This ensures that information is always protected throughout its journey.
The connection between networks occurs smoothly, just as if offices or branches were working on the same local network. The gateway at each network end performs the function of encrypting and decrypting data, keeping information safe as it passes through and reaches its destination.
4. Comparing VPN Site to Site with VPN Client to Site
VPN Site-to-Site connects the networks of remote offices, creating a linked internal network, while VPN Client-to-Site allows individual users to securely access the corporate network remotely. Each solution is suitable for different purposes and organizational scales.
| Features | VPN Site-to-Site | VPN Client-to-Site |
| Purpose of use | Connecting LANs between different offices/branches | Connection between a personal device and an internal network |
| Target users | Businesses with multiple branches or offices | Individual users or remote employees |
| Connection method | Automatically connects between networks without user intervention | Users install VPN software and connect manually |
| Security | Data is encrypted through a secure tunnel between networks | Data is encrypted from the personal device to the internal network |
| Connection management | Requires installation and management at the network gateways of each location | Users manage their own connections via VPN software |
| Complexity | Complex configuration and maintenance, suitable for large organizations | Easy to install and use for individual users |
>>>> REFER NOW:
- What is iTop VPN? How to install and use iTop VPN 2026
- What is Cloudflare WARP? Benefits and installation guide
5. Strengths and limitations of VPN Site to Site
VPN Site to Site provides a secure and stable connection between offices or branches, helping to share network resources efficiently and securely. However, it requires complex configuration and high technical management, and may face difficulties in maintaining a stable connection if the network infrastructure does not meet the requirements.
| Strengths | Limitations |
|
Provides secure connections Ensures security between offices and branches |
Complex configuration Requires high technical expertise |
|
Allows resource sharing Offices can share resources like a single LAN |
Strong infrastructure requirements The network must be stable |
|
Reduces branch networking costs Lowers the cost of setting up individual private networks for each branch |
High deployment costs Requires significant investment in hardware and software |
|
High stability Operates automatically without user intervention |
Time-consuming expansion Adding new branches requires significant time to reconfigure the system |
6. Security of VPN Site to Site
VPN Site to Site provides a high level of security by using encrypted tunnels to transmit data between networks, helping to protect information from intrusion and monitoring by third parties. Below are some factors that enhance the security of VPN Site to Site:
- Strong encryption: Data is encrypted using strong encryption protocols such as IPsec or SSL/TLS, helping to prevent data leakage or reading when transmitted over the Internet.
- Strong authentication: Uses authentication methods such as IP addresses, digital certificates, or key pairs to ensure that only authorized networks can connect with each other.
- Firewalls and access control: VPN gateways are protected by firewalls and access control measures, allowing only valid connections to be transmitted through the network.
- Ensuring data integrity: VPN protocols often use data integrity checking methods like HMAC (Hash-based Message Authentication Code) to ensure that data is not altered during transmission.
- Intrusion detection and prevention: Some VPN Site to Site systems can integrate monitoring and intrusion detection/prevention measures (IDS/IPS) to track and block suspicious behavior.

VPN Site to Site provides a high level of security
Thus, Hidemyacc has provided you with information about VPN Site to Site and a comparison between VPN Site to Site and Client to Site. Compared to VPN Client to Site, VPN Site to Site offers better security and more stable performance, helping to optimize a business's network system. Good luck in choosing the right network connection solution!
>>>> RELATED ARTICLES: