Using a VPN to change your IP address is a popular way to access geo-blocked content and manage multiple accounts. But here’s the catch — if VPN detection kicks in, a website may limit your access or even suspend all linked accounts. So, how exactly do websites detect VPNs? And is there a smarter way to stay hidden while staying in control? Let’s dive into the answers in this blog post.
1. How do websites detect you are using a VPN?
Are you wondering how websites detect if you are using a VPN and which methods they employ? Here are five ways websites can easily identify VPN usage for IP address changes:
Blacklisting known VPN IP address
Every device connected to the Internet has an IP address. Websites maintain lists of known VPN server IP addresses. If your IP address falls within these ranges, it raises suspicion that you are using a VPN to access the website.
Additionally, since VPNs have numerous customers, they generate a high volume of data. Home IP addresses and even public free Wi-Fi generate much less data than a VPN server. If many customers are simultaneously using the same IP address, websites may infer that a VPN is the source of this traffic.
DNS leaks
Not only do devices connecting to the Internet have IP addresses, but websites also have their own IP addresses. Instead of entering the IP address of a website to access it, users can enter the DNS (Domain Name System) of the website.
Many VPNs use their DNS servers and have built-in protection to prevent requests from leaving the encrypted VPN tunnel. A DNS leak occurs when the user's DNS requests move outside the encrypted tunnel, making their browsing activity, including their IP address, location, and web searches, visible to their ISP.
Timezone mismatch
When users use a VPN to connect to websites in different geographic regions, a timezone mismatch can occur.
For instance, a user from the United States browsing a website may appear to be browsing from Vietnam due to the VPN server's location. This significant deviation raises suspicions that you are attempting to hide your IP address by using a VPN.
Timezone mismatches can be resolved by adjusting the timezone on your device. If you overlook the timezone setting, websites can easily discern that you are using a VPN.
Port blocking
Many VPNs use specific ports, and websites may perform port scanning to identify common VPN protocols or ports associated with VPN traffic. Detection of these protocols or ports can raise suspicions of VPN usage.
Browser geolocation
Browsers may be configured to disclose your location to websites. If your browser is set to do so, change the setting. If your browser reveals your actual location in opposition to your VPN's server, it signals to the website that you are using a VPN to change your IP address.
2. VPN vs Proxy: Which is the best choice?
When it comes to changing your IP address, two common methods are VPNs and proxies. Let's explore the differences between these options to help you make an informed choice.
Similarities
Firstly, both proxies and VPNs serve the purpose of changing your IP address. Utilizing either of them allows you to conceal your actual IP address and present yourself as a user from a different location. This proves beneficial when accessing websites or platforms that may restrict traffic from specific locations or regions. By changing your IP address to a permitted location, you can overcome such restrictions.
Differences
Despite both methods serving the same purpose, there are two key distinctions between proxies and VPNs.
Connection handling
- Proxy: Enables users to establish multiple connections simultaneously. Users can purchase proxies, and add them to profiles to change IP address. You can employ proxies for various purposes such as selling on e-commerce sites, web scraping, and managing social accounts.
- VPN: Primarily used for personal purposes to enhance online security.
Security considerations
- Proxy: When using a residential proxy, you can blend in as a regular individual residing in a specific neighborhood. Combining a VPN with a proxy can provide an extra layer of security for your accounts.
- VPN: While a VPN allows you to change your IP address and access websites, it's worth noting that websites can easily detect VPN usage. The security of a VPN is considered lower compared to a proxy. It is generally recommended to use a combination of VPN and proxy for enhanced security, rather than relying solely on a VPN.
In summary, the choice between a VPN and a proxy depends on your specific needs. If you require multiple connections for diverse purposes, a proxy might be the preferred choice. However, if personal online security is your primary concern, using a VPN, possibly in conjunction with a proxy, is advisable to ensure a more comprehensive protection of your accounts.
3. Why changing IP address is not enough to protect your online privacy?
While changing your IP address is a common practice to safeguard your identity while browsing, it may surprise you to learn that it's not sufficient for ensuring online privacy. Websites and platforms employ a technique called browser fingerprinting to gather unique identifiers from devices accessing their sites. Similar to a human fingerprint, each device possesses its browser fingerprints, encompassing details such as operating system, browser type, hardware specifications, device memory, screen resolution, location, time zone, language, and more.
Even if you change your IP address, websites can still identify you based on these browser fingerprint parameters. This is why, despite altering your IP address, websites may detect if you are using multiple accounts on the same device.
To address this concern, you can employ various methods to change your browser fingerprint:
- VPS (Virtual Private Server): Utilize a VPS to modify your browser fingerprint.
- Privacy Extensions: Install privacy extensions that help alter and snoof browser fingerprint details.
- Antidetect Browser: Use an antidetect browser, which allows users to create multiple browser profiles, each with different browser fingerprints. This is especially useful for those managing multiple accounts on the same device.
The most effective approach involves combining proxies and antidetect browsers. Antidetect browsers enable users to create distinct browser profiles, each with its unique fingerprint, and use them on the same device. By adding proxies to these profiles, they appear as independent devices with distinct Internet connections.
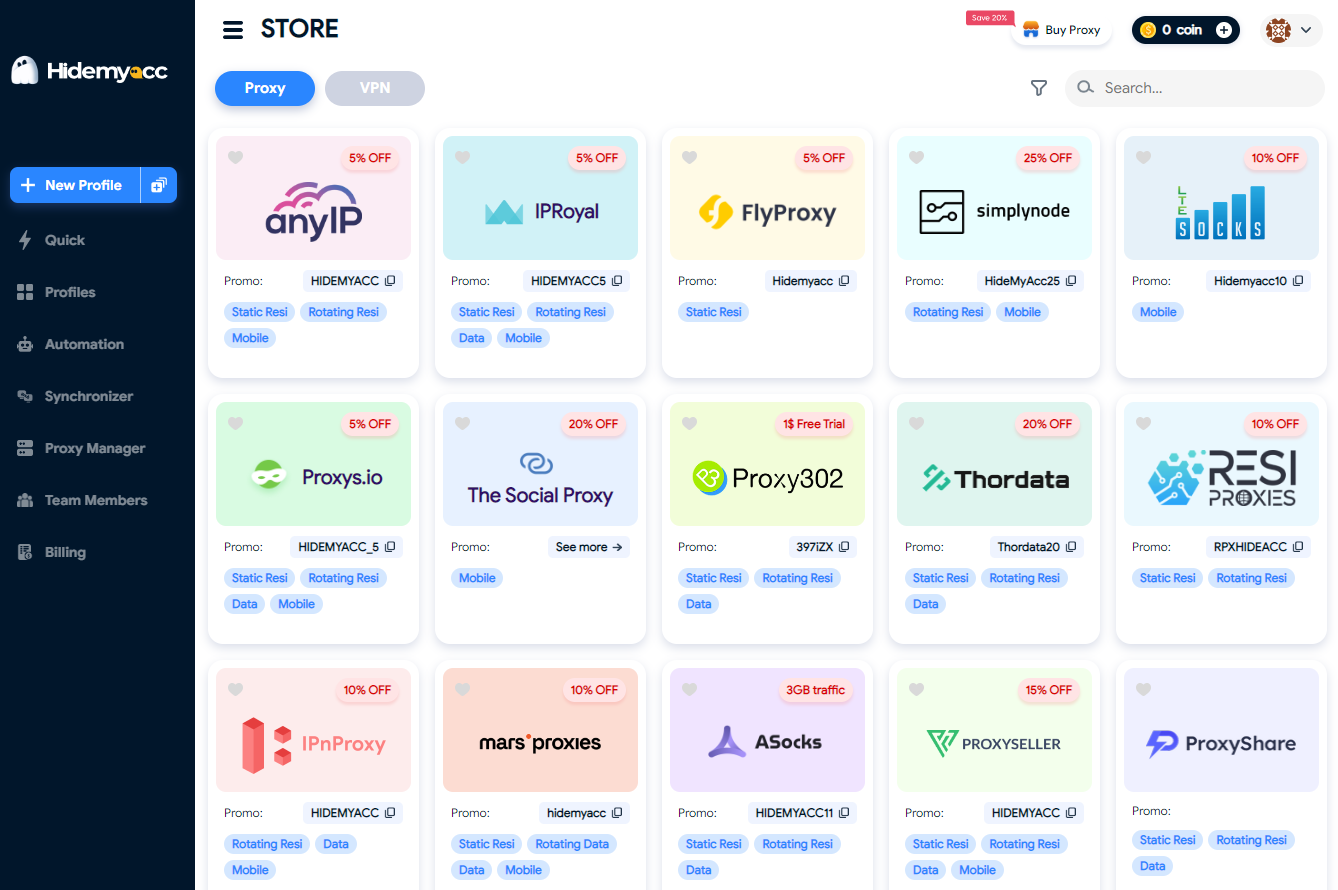
4. ntidetect Browser Hidemyacc - The best solution to change the browser fingerprint
Hidemyacc offers a comprehensive solution to address these privacy concerns. Besides its notable features catering to various user needs, Hidemyacc provides a Proxy Store showcasing trustworthy proxy providers in the market. Users can access exclusive discounts (up to 50%) from these providers through Hidemyacc, allowing them to purchase high-quality proxies at a more affordable price. This combination of an antidetect browser and reliable proxies enhances online privacy, making it an ideal solution for those requiring multiple account management on the same device.
5. Conclusion
While VPNs are widely used, VPN detection by websites can result in blocked access or even account suspensions—posing a major risk, especially for users managing multiple accounts. A more effective and sustainable solution is combining proxies with an antidetect browser to fully mask your digital identity.
With Hidemyacc, you can create separate browser profiles, rotate proxies easily, and manage multiple accounts on one device without triggering red flags. Plus, you can connect with trusted proxy providers right inside the platform—convenient and cost-effective.
Try Hidemyacc free for 7 days and see how it can protect your operations. Need help? Reach us anytime via Telegram, Skype, or Facebook Messenger.