Have you ever wondered what is antidetect browser and how it protects your online identity? In simple terms, an antidetect browser is a specialized tool that allows users to customize their digital fingerprints to browse the web with multiple, isolated profiles. Unlike standard browsers, it provides a layer of anonymity that goes beyond VPNs. In this guide, we will explore the definition of antidetect browser, its core mechanisms, and why it has become an essential tool for multi-accounting and digital marketing.
1. What is antidetect browser?
An antidetect browser is a specialized web browser based on Chromium or Firefox engines that allows users to create and manage multiple, isolated browsing profiles on a single device. Each profile functions as a unique digital identity by customizing and masking its browser fingerprint - a collection of technical data points such as User-Agent, WebGL, Canvas, IP address, and hardware configurations. This allows for the emulation of different hardware configurations to ensure privacy.
Unlike standard browsers (like Chrome or Safari), an antidetect browser ensures that websites and anti-fraud systems cannot link your different profiles to the same person or device. This technology is essential for professionals who need to manage multiple accounts for marketing, dropshipping, or privacy without being flagged or banned by platforms like Facebook, Google, or Amazon.
2. The core technology: How do antidetect browsers work?
To answer the question what is antidetect browser, it’s important to first understand how websites identify and track users today. Modern platforms no longer rely solely on cookies or IP addresses. Instead, they use browser fingerprinting an advanced tracking technique that collects hundreds of device and browser signals to generate a unique digital identity for each user.
So, what is an antidetect browser in practice? It is a tool designed to simulate independent browsing environments by isolating fingerprints across multiple profiles. Rather than simply hiding your IP, it creates distinct virtual identities that appear as separate devices to websites.
Below is a technical breakdown explaining how this mechanism works and why it helps maintain anonymity at scale:
2.1. Browser fingerprint emulation & customization
Rather than simply blocking tracking scripts which often raises suspicion, this technology focuses on replicating realistic, widely used browser fingerprint. Key browser and device attributes are adjusted so each profile appears to originate from a completely different machine.
- Canvas & WebGL signals: Rendering outputs are subtly altered or injected with controlled randomness, making it difficult for websites to recognize the underlying GPU or graphics stack.
- AudioContext signatures: Audio processing behaviors are adjusted so audio fingerprints remain inconsistent across different profiles.
- Hardware-level spoofing: System-reported details such as CPU threads, RAM size, screen resolution, and operating system are modified to resemble common devices (for example, simulating a MacBook or mobile device from a desktop setup).
2.2. Profile isolation & secure sandboxing
Every browsing profile runs inside its own isolated environment, preventing cross-contamination between identities.
- Cookies & local storage: Each profile maintains a separate storage space, ensuring login sessions, cookies, and cached data never overlap.
- WebRTC leak prevention: Internal communication protocols are controlled to stop real IP information from being exposed, even in scenarios where a VPN is not active.
2.3. Proxy integration & location consistency
While fingerprint emulation handles device-level signals, network identity still depends on IP routing, which is why proxy integration is essential.
-
Location alignment: Advanced solutions automatically synchronize timezone, browser language, and WebRTC settings with the proxy’s geographic location. For example, if the IP resolves to New York, system-level signals are adjusted accordingly to avoid detection inconsistencies.
2.4. Handling server-side detection signals
Beyond client-side fingerprints, major platforms also evaluate deeper indicators such as TLS handshakes and User-Agent coherence. Tools like Hidemyacc rely on customized browser cores built on Chromium or Firefox to ensure these low-level signals remain stable and realistic, matching the emulated device profile from end to end.
3. Key technical components of a reliable antidetect browser
Not all antidetect browsers are created equal. While many claim to offer anonymity, a truly reliable tool must integrate several core technical components to ensure your profiles remain undetectable by modern anti-fraud systems. When researching what is antidetect browser software, look for these five essential pillars:
3.1. Deep fingerprint parameter customization
A high-end antidetect browser doesn't just block tracking; it provides a sophisticated interface to modify every layer of your digital identity. This includes low-level parameters such as:
- Hardware Signatures: CPU cores, RAM size, and Device Memory.
- Graphic Identifiers: Canvas, WebGL metadata, and Font rendering.
- Media Devices: Masking the number of connected microphones, cameras, and speakers. The goal is to create a "natural-looking" profile that blends in with millions of regular internet users.
3.2. Seamless proxy support & management
While the browser handles the "device" identity, the Proxy handles the "location" identity. A robust antidetect tool must offer:
- Proxy Managers: The ability to import and assign proxies (SOCKS5, HTTP) to specific profiles easily.
- Automatic IP Validation: Checking if the proxy is active and showing its geolocation before launching the profile.
- Timezone & WebRTC Alignment: Ensuring the browser's internal clock and WebRTC settings automatically match the Proxy’s IP to prevent data mismatches.
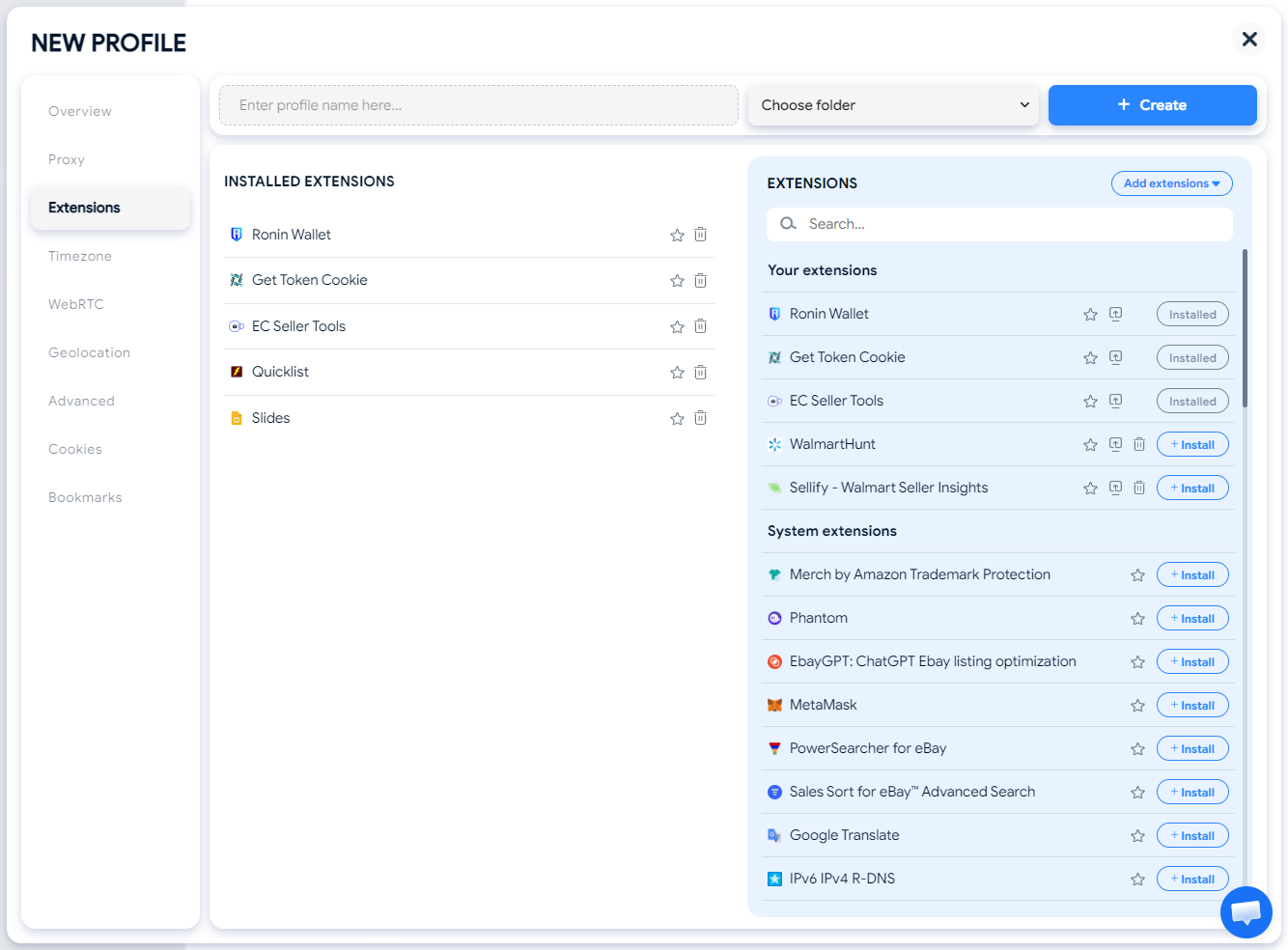
3.3. Isolated sandboxing for cookies and extensions
To prevent "cross-profile tracking," a reliable browser must utilize advanced Sandboxing technology.
- Isolated Storage: Each profile stores its own cookies, cache, and history in a separate folder that other profiles cannot access.
- Extension Management: The ability to install specific Chrome or Firefox extensions on a per-profile basis without them interfering with each other.
3.4. Native browser automation frameworks
Efficiency is a critical factor for professionals managing hundreds of accounts. A high-quality antidetect browser serves not just as a privacy tool, but as a powerful automation engine with two distinct approaches:
For developers (coded automation): A technical-grade antidetect browser must offer seamless integration with industry-standard frameworks like Puppeteer, Playwright, or Selenium. Through a local API, developers can write scripts in languages like Python or JavaScript to automate complex workflows (e.g., data scraping, bulk account warming) while maintaining the integrity of each profile's unique fingerprint.
For non-tech users (No-code automation): Modern tools now feature RPA (Robotic Process Automation) and No-Code Scenario Builders. These allow users to create automation flows using a visual, drag-and-drop interface, no programming skills required.
- Common use cases: Automatically liking posts, following users, "warming up" cookies by visiting random websites, or even automated checkout for dropshipping.
- Synchronizer: Some browsers also offer a "synchronizer" feature, where actions performed in one window (typing, clicking) are mirrored instantly across dozens of other open profiles, effectively multiplying your productivity.
3.5. Collaborative infrastructure for team management
For agencies and large-scale operations, data security during teamwork is vital.
- Profile Sharing: Securely transferring profiles to team members without triggering security alerts due to device changes.
- Permission Control: Granular settings to manage who can edit, launch, or delete specific profiles, ensuring that your digital assets remain protected at all times.
4. Antidetect browser vs. VPN vs. Incognito mode: Understanding the hierarchy of privacy
Many users mistakenly treat these tools as interchangeable. However, in the eyes of an anti-fraud system (like Google's Picasso or Facebook's Lander), there is a massive difference between hiding your location and spoofing your identity.
4.1. Incognito mode: The "local" privacy fallacy
Incognito mode is designed for your physical environment, not the internet. It ensures that anyone using your computer won't see your history or cookies.
- Why it fails for multi-accounting: It does not change your IP, nor does it alter your Browser Fingerprint. Websites can still "see" your hardware configuration, OS version, and fonts, making it trivial to link your "Incognito" session to your regular one.
- Best for: Avoiding local tracking on shared devices.
4.2. VPN: The "location" mask with a "fixed" identity
A VPN (Virtual Private Network) is an essential part of a secure internet infrastructure. It excels at encrypting your data tunnel and masking your IP address to provide basic network anonymity.
- The "Dirty IP" & Fingerprint gap: While a VPN changes your location, it doesn't touch your device parameters. If you log into 5 different accounts using 5 different VPN locations but the same browser, the website sees the exact same Canvas, WebGL, and Audio signatures. To their security system, this looks like one person traveling across the world in seconds a major red flag.
- Best for: Bypassing geo-blocks and basic IP anonymity.
4.3. Antidetect browser: The "identity" architect
An antidetect browser (like Hidemyacc) operates at the kernel and API level of the browser. It doesn't just hide; it replaces.
- The Holistic Defense: It allows you to create a unique Digital Twin for every account. When combined with a high-quality proxy, you are changing both the Network Layer (IP) and the Application Layer (Fingerprint).
- Verdict: It is the only tool that creates a "stateless" environment where each profile is perceived as a unique, legitimate physical device.
| Feature | Incognito Mode | Standard VPN | Antidetect Browser |
| Masks IP address | ❌ No | ✅ Yes | ✅ Yes (via Proxy) |
| Clears local cookies | ✅ Yes | ❌ No | ✅ Yes (Isolated per Profile) |
| Spoofs hardware (Canvas/WebGL) | ❌ No | ❌ No | ✅ Full Control |
| Media device masking | ❌ No | ❌ No | ✅ Yes |
| Automated warm-up | ❌ No | ❌ No | ✅ Yes (RPA/Synchronizer) |
| Risk of account llinking | 🚨 Extreme | ⚠️ High | 🛡️ Very Low |
5. Why should you use an antidetect browser? (Primary use cases)
The versatility of antidetect technology makes it a cornerstone for various online business models. If your work involves interacting with platforms that have strict anti-fraud or "one-person-one-account" policies, understanding what is antidetect browser utility in your specific niche is vital.
5.1. Managing multiple social media accounts (Facebook, TikTok)
Social media giants use advanced tracking to ensure each user only operates one personal account. For agencies managing dozens of clients, this is a major hurdle.
- The Challenge: Logging into multiple social media accounts from the same browser leads to "Chain Bans" where one account's violation gets all others suspended.
- The Antidetect Solution: Each profile acts as a separate mobile or desktop device with its own unique history and parameters. This allows social media managers to scale their operations without the platforms ever linking the accounts together.
5.2. E-commerce & dropshipping (Amazon, eBay, Etsy)
In the competitive landscape of online retail, diversification is the key to long-term survival. For many entrepreneurs, testing a new ecommerce business idea often requires setting up "stealth accounts" to explore different product niches or to create a safety net in case a primary store faces unexpected issues..
- The Challenge: Amazon and Etsy track hardware IDs and browser signals very aggressively. If they detect a link between a suspended store and a new one, the new one is closed instantly.
- The Antidetect Solution: By emulating different hardware configurations for each store, you can run multiple "stealth" businesses globally, ensuring that each storefront remains a completely independent entity.
5.3. Affiliate marketing & Ad verification
Affiliate marketers rely on running multiple ad accounts (Google Ads, Bing Ads) to test creatives and scale winning campaigns. For many, this is the most effective way to make money online at a professional scale.
- The Challenge: Platforms often flag accounts that appear to be coming from the same machine, especially if those accounts are running similar ads. Additionally, marketers need to verify how their ads appear in different countries.
- The Antidetect Solution: It allows you to check your ads from a "clean" local profile in any country, ensuring that your tracking links are working and your ads aren't being hidden by competitors or fraudulent publishers.
5.4. Web scraping and data collection
Modern websites have sophisticated anti-bot protections (like Cloudflare or Akamai) that can detect and block automated scraping tools.
- The Challenge: Standard scrapers have a "robotic" fingerprint that is easily identified, leading to IP bans and CAPTCHA loops.
- The Antidetect Solution: By using an antidetect browser, your scraping scripts (via Puppeteer or Playwright) appear to be coming from a real, organic user on a legitimate device. This significantly increases the success rate of data extraction and reduces the need for expensive proxy rotation.
6. The pros and cons of implementing antidetect technology
Every professional tool has its trade-offs. While an antidetect browser is a game-changer for digital operations, it is important to understand both its immense value and the practical challenges you might face when integrating it into your workflow.
6.1. Advantages for professional workflows
The primary reason businesses invest in antidetect technology is the return on investment (ROI) through security and efficiency.
- Risk Mitigation: The biggest "Pro" is the prevention of Account Linking. By creating "firewalls" between your profiles, you protect your entire business assets from being taken down by a single account's mistake.
- Massive Scalability: With features like No-code Automation and Synchronizer, a single operator can manage 100+ accounts as easily as one, multiplying productivity without increasing headcount.
- Cost-Efficiency in the long run: While the software has a subscription cost, it is significantly cheaper than the losses incurred from frequent account bans, buying new hardware, or paying for expensive residential proxies that get burned by poor fingerprinting.
- Global reach: It allows teams to "virtually" relocate their business to any country, making it indispensable for international dropshipping and affiliate marketing.
6.2. Potential limitations and learning curves
To provide a helpful perspective, users should be aware of the following:
- The Learning Curve: Unlike a standard browser, an antidetect browser requires a basic understanding of how digital fingerprints and proxies work. Incorrectly configuring a profile (e.g., mismatching a US proxy with a Vietnamese timezone) can still trigger security flags.
- Dependency on Proxy Quality: An antidetect browser is only "half of the armor." If you use poor-quality, blacklisted, or free proxies, even the best fingerprint spoofing cannot save your account from being flagged at the network level.
- Resource Consumption: Running multiple isolated browser profiles simultaneously requires more RAM and CPU power than a standard Chrome window. Users with older hardware might experience performance lag when opening many profiles at once.
- Subscription Costs: For beginners or hobbyists, the monthly cost of a premium antidetect browser plus high-quality proxies can be a barrier compared to free (but risky) alternatives.
7. Top 5 antidetect browsers to consider in 2026
When you understand what is an antidetect browser and how it functions, the next step is choosing a reliable provider. The market has evolved significantly, but these five tools remain the industry leaders for providing stable, isolated environments.
7.1. Hidemyacc: Best for efficiency and stability
For those looking for the best all-around solution, Hidemyacc is the most optimized antidetect browser for both beginners and pros. It is designed to simplify the complex process of fingerprint masking while maintaining high success rates against the world's toughest anti-fraud systems.
- Key Strengths: It offers a massive database of real, fresh fingerprints and a high-performance Synchronizer. This makes it the perfect answer for anyone asking what is antidetect browser software that can handle hundreds of accounts with zero lag.
- Best For: Marketing agencies, dropshippers, and crypto hunters who need a stable, long-term solution.
7.2. Multilogin
As a pioneer in the industry, Multilogin has helped define the standards of what is antidetect browser technology today.
Quick Review: Highly secure with proprietary browser engines (Mimic and Stealthfox). While it is an enterprise-grade tool, its premium pricing might be steep for solo users.
7.3. Gologin
Gologin focuses on making the concept of what is antidetect browser accessible to everyone through a simple, user-friendly interface.
Quick Review: It provides a great cloud-based ecosystem and a mobile app. It’s ideal for users who need a straightforward setup without too many technical hurdles.
7.4. Adspower
Adspower is a strong contender, especially for users who prioritize automation within their antidetect browser workflow.
Quick Review: It features an extensive RPA (Robotic Process Automation) store. It’s a powerful choice if your primary goal is automating e-commerce tasks across multiple profiles.
7.5. Dolphin Anty
Dolphin Anty that shows another side of what is antidetect browser utility, specifically for the affiliate marketing (traffic arbitrage) niche.
Quick Review: It includes built-in features for Facebook and TikTok ad management, allowing teams to track ad statuses directly within the browser interface.
>>> Other reviews of antidetect browsers
- Antidetect Browser Kameleo review: Is it worth using?
- MoreLogin Browser: Detailed Review and Alternatives
- Incogniton Browser: Honest Review
- BitBrowser: Detailed, hands-on review
- VMLogin Review - Is it an efficient antidetect browser?
- Is Linken Sphere the Right Antidetect Browser?
- SessionBox review: Honest look at its features & limits
- Ghost Browser in-depth review: A multi-session browser
- Nstbrowser Review: Affordable, but is it powerful enough?
- Is Lalicat a good antidetect browser? Full review & real testing
- Octo Browser: Full Review for Multi-Account Management
- Is Undetectable the right antidetect browser for your needs?
- ixBrowser review: How does it work and is it good for multi-account?
- Is DICloak a reliable antidetect browser? Pros & cons!
- What is the best FREE antidetect browser for multiple accounts?
8. Selection guide: How to choose the right tool for your needs
After understanding what is an antidetect browser and reviewing the top market leaders, the question remains: Which one should you choose? Selecting the wrong tool can lead to leaked fingerprints and wasted budget.
To find the perfect fit, evaluate your options based on these four professional criteria:
8.1. Browser engine and fingerprint database
The heart of an antidetect browser is its engine (usually Chromium or Firefox).
- Check for updates: Websites update their tracking algorithms weekly. Your chosen browser must update its engine and fingerprint database just as frequently.
- Real Fingerprints: Ensure the tool uses fingerprints from real devices, not just randomly generated data, which can easily be detected as "artificial."
8.2. Ease of use vs. automation depth
Your choice should match your technical skill level:
- For Beginners: Look for a clean UI, a "Quick Create" profile feature, and an active support team.
- For Power Users: Check if the tool supports No-code RPA or has a robust API for Puppeteer/Selenium. A good antidetect browser should save you time, not add more complexity to your day.
8.3. Team collaboration features
If you are an agency, the ability to share profiles securely is non-negotiable.
- Permission Management: Can you limit who can see or edit specific profiles?
- Cloud Sync: Can team members access the same profile from different locations without triggering a security alert?
8.4. Stability and support
When managing hundreds of accounts, a single bug can be disastrous.
- System Stability: Look for a tool that doesn't crash or lag when multiple profiles are open.
- Customer Support: In the fast-moving world of multi-accounting, you need a support team that answers in minutes, not days.
9. Conclusion
By now, the answer to "What is antidetect browser?" should be clear: it is your digital invisibility cloak and your most powerful tool for scaling online operations. In a world where your digital footprint is your identity, taking control of that footprint isn't just an advantage, it's a necessity.
Ready to see it in action?
Download Hidemyacc for free today and start your first 30 secure profiles. Experience the future of multi-accounting with the most stable antidetect solution on the market.
Try for FREE10. FAQ
Is using an antidetect browser legal?
Yes, antidetect browsers are completely legal software tools. They are essentially privacy-focused browsers that give you control over your own data. However, legality depends on how you use them. Using them for market research, ad verification, or managing multiple legitimate business accounts is standard practice. Using them for illegal activities (fraud, hacking, etc.) remains a violation of the law.
Do I still need a proxy if I use an antidetect browser?
Absolutely. An antidetect browser masks your "Identity" (Hardware/Software signals), while a proxy masks your "Location" (IP Address). To achieve true isolation, you must use both. Without a proxy, all your unique browser profiles will still show the same home or office IP address, leading to instant account linking.
Can websites like Facebook or Amazon detect I am using an antidetect tool?
Modern anti-fraud systems are incredibly sophisticated. However, a high-quality browser like Hidemyacc uses "Real Canvas" and "Real WebGL" technology. Instead of just blocking trackers, it provides the website with plausible and consistent data. As long as your browser fingerprint matches your proxy's location and your user behavior is organic, these platforms will see you as a regular user.
Is an antidetect browser the same as a virtual machine (VM)?
No. While both provide isolation, a VM emulates an entire operating system, which is very resource-intensive (heavy on RAM/CPU). An antidetect browser is much more efficient; it isolates the browser environment only, allowing you to run dozens of profiles on a standard laptop where a VM could only handle two or three.
Can I use a free antidetect browser?
There are free versions (like the 5-profile starter plans), but you should be cautious of "cracked" or completely free software from unknown sources. Your browser handles sensitive data (passwords, cookies, sessions). Using a non-reputable tool puts your accounts at risk of being stolen or leaked.